Learn Exactly How We Made diskgenius review Last Month
Massachusetts Institute of Technology
John recently diskgenius review won the DevNet Creator Award for all ofContinue reading “Ep 71 – Merlin the Auto Magician”. Students have the opportunity to select from program specializations in informatics, network security, and geographic information systems, or concentrate on the enhancement of skills for advanced Cisco certifications. But remember, on top of everything, always focus on becoming a better network professional, and the money will follow. Here are some basic concepts of computer networking. I highly recommend them over anyone else in the area. This will include consideration of wider issues and the ability to manage activities and resources, as well as generate, implement, and report on solutions to meet task objectives. For example, it increases your chances of being able to transfer coursework to another school and helps you qualify for graduate programs. A computer networking degree is an undergraduate program that prepares students to work in the information technology field. Read more about the CNIT program partners below. Free eBook: Salesforce App Builder Study Guide. Alex Saroyan 00:02:43: I knew how to program, and I’ve improved my programming skills over time just to start automating my regular network engineering things. You may work for a company on site or visit a company when needed, like before a site upgrade.

Are Free Online Networking Courses Worth It?
They are responsible for maintaining and repairing computer networks. CompTIA foundational and networking certifications are designed to be stacked, as each certification builds upon and relates to the others. Some even have company profiles with reviews by staff. Cellular Networking: This topic covers the technology and protocols used to provide wireless communication between devices via cellular networks. You will also complete a capstone project that represents the culmination of all your hard work. Are you just getting started in IT or in an entry level role and thinking about your next move. Upon completion of all CompTIA exams above, students also earn CompTIA Secure Infrastructure Specialist Certification. Thus, the end to end delay is L/R1 + L/R2. This is a Bachelor of Technology option in Information Technology. The US Bureau of Labor Statistics BLS reports that the job outlook for network and computer systems administrators is growing at five percent, which is a slower growth rate than the average of eight percent. If you’re just starting out, this is a certification for you. Knowing the details of these technologies and the specifics of how each one works, will help you choose the best type of network for your needs. Network Programmer is one of the trending job profiles in the Networking Industry. You can easily increase your pay by learning new skills or getting more experience. For example, World Wide Web servers operate on port 80, and email relay servers usually listen on port 25. Students who hope to participate in this field may study the software and hardware needed to create these systems.
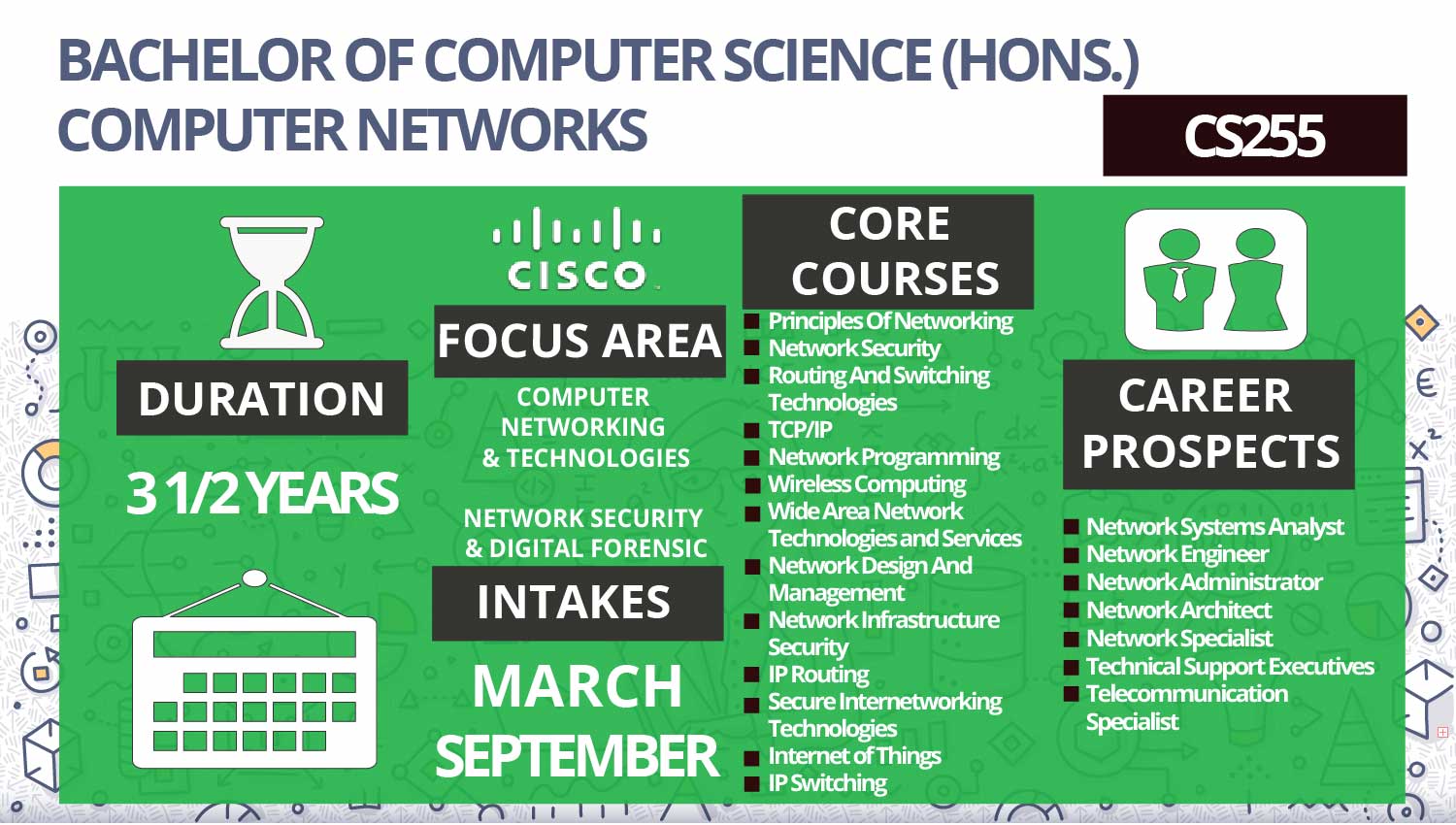
Facilities
If you wish to take the Juniper certification exam, then you should know that topics like cloud, security, datacentre, etc. Curriculum: Intermediate. This network is used as it allows the user to transfer or share data, files, and resources. An omnidirectional antenna creates a strong signal strength throughout your property. Many protocols would do the trick. That’s how it should be. Ultimately, however, career success will be down to the graduate’s ability to work under pressure. Understanding Switch Mode Power Supply SMPS. Data transmission over the network connections occurs in one direction. Thus, it is essential to develop communication skills as it will be possible to cater to non tech savvy audiences. In Achim Rettberg, Mauro C. Following are the protocols used over here. Coursework includes Fundamentals of Information and Cybersecurity, Microcomputer Applications, Cybersecurity Investigations, Systems Analysis, Computer Architecture, and more. Clearly, earning CompTIA Network+ is a good move. Before it, people entering the networking field had to immediately choose between going for one of those major certifications or the other. A bachelor’s degree is a three or four year undergraduate degree and is the standard for higher education throughout most of the world. Author Name: Rich Seifert. The need for strong, secure networking solutions has never been greater. Thus, the hiring process is competitive. A Network Engineer plans, implements, and oversees a network. The first year consists of various mandatory and fundamental learning activities, while activities in the second year are mostly elective. Validate expertise needed to deliver on cloud initiatives using AWS.
What Can You Do with an Online Computer Networking Degree?
SQL – Structured Query Language is a database access language. There are several types of computer networks. Hopefully the generated list of term related words above suit your needs. Students will receive an introduction to the principles of information processing and an overview of the information technologies for digital data processing using computational and communication devices, including an initial understanding of the requirements for usability, quality, complexity, security and privacy of the developed solution. Kai Hwang, University of Southern California USA. According to a study from Burning Glass Technologies, there were 147,448 network professional job postings between 2019 and 2020. An organization that provides services for accessing the Internet. Network Analytics and Troubleshooting teaches students to use network monitoring and analytics tools and practices that are common in the workplace in order to troubleshoot and fix complex computer networks. This module tackles all issues important in the design, implementation, and configuration and troubleshooting of routing protocols in computer networks. Once you’ve obtained your core exam, you can then choose from one of the following six exams, which cover specializations like network design, wireless, and automation. Plus, you can balance your studies with work and family commitments to make your dreams a reality. Students will attend lectures and workshops, undergo red and blue team training, and participate in cyber attack simulations. =NL/R + P 1L/R = N+P 1L/R. Quality of Instruction: Excellent.

Industrial network security
You can download this image easily and for free. IT leaders at Enterprise Connect discuss their strategies for successful hybrid working, from transparent team agreements to. Besides a degree, many employers preferred a specialization degree in this job role related to the industry or field of network engineering. Estimated: $15 an hour. Every bit of information sent over the internet doesn’t go to every device connected to the internet. This provides students with invaluable job experience, financial assistance, and contacts for potential full time jobs after graduation. WGU’s expertly designed network engineering bachelor’s program can help you gain the unique technical skills you need to succeed. We’re going to improve the consistency because, looking into our traditional network engineering history, and we know that most of the failures are related to inconsistencies. Segregation improves security and lets you classify your networks by function. You’ll likely need to enroll in a degree program to become a network and computer systems administrator. The higher the kbps means more the bits transferred per second, more the speed, faster the network/connection. So, the deadlines are flexible. 1920×1200 16:10 aspect ratio. Time to Complete: Five weeks. Search for your program below and contact directly the admission office of the school of your choice by filling in the lead form. If you’re still wondering what you can do with a computer networking degree, you may be wise to consider the position of a computer systems analyst. Required fields are marked. Recall that there are 4 circuits on each link. For example, if a router has translation functionality, it becomes a router. Cyber security is the body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access. Although the road to obtaining a CCIE is long and hard, it is well worth the effort, time, and money. For this course, you must have taken CS110 or an equivalent course. 5 Summary of Findings 51. 6 Throughput Throughput refers to actual measured bandwidth, at a specific time of day, using specific Internet routes, and while a specific set of data is transmitted on the network. This is also sometimes called the data rate. The degree program has eight technology related majors and it is offered purely online through computer based learning systems and courses that coincide with the traditional programs on campus. The time required for a signal or bit to travel from one point to another is Propagation Time. Network administrators and computer systems administrators may work closely with other IT professionals. Which feature should be configured.
Performance Cookies
Although WAN networks are complex, they are frequently utilized in mobile communications because they can span great distances. Computer Organization. It’s credited worldwide and considered one of the most prestigious networking certificates in the IT industry. ICMP stands for internet control message protocol. The LMSC has made more than 70 standards for IEEE 802. Is there a new way to solve the preceding problems. One of our top choices for free online networking courses. Ruckus Wireless Access Points. Hypertext Transfer Protocol HTTP. The advantage of UTP is a low cost, very simple to install, and high speed. 3 of packet switching versus circuit switching in which an example is provided with a 1 Mbps link. Let users communicate via email, video chat, etc. Hubs connect multiple computer networking devices together. Possible ability to record and replay sessions. The hardware professionals are always taking care the maintenance of computer hardware, while networking involves connecting a group of 2 or more computer systems for sharing data and information. My co founder and I, did a couple of experiments. Explain the function of hubs, switches, and routers. Following are the technologies classified as home, small office, enterprise or wide area wireless access. Third dimension: flexible combination of optional TLVs following segment lists. This part time bootcamp covers offensive security, defensive security, and standard security operations for organizations. In this architecture, the cloud infrastructure is provisioned on the organization’s premises but hosted in a third party data center. Following is the list of hardware’s required to set up a computer network.
Comment about this article, ask questions, or add new information about this topic:
Certificate: Yes, with a fee. The Cisco YouTube channel features videos on learning networking, big data, and network security. Do you want to earn a networking certification but you don’t know how to prepare yourself for the exams. I thought it was scam ooo. Typically, routers are placed on the backhaul network, and they in turn may have their own backhaul networks that serve many edge devices. Taking advantage of short term programs is ideal for anyone looking to make a difference in this field. We will send you an one time password on your mobile number. Bind”,serverPortserverSocket. Assume a propagation speed of 100 km/hour. At UC, we support you on your individual path. Yes, then Network Programming is just for you. Excel the field of networking by creating and executing networking configurations at your best. Your career path will depend, to a certain extent, on the size of the organisation you work for and the scope of its IT systems. Ready To Build Your Resume. When you click through from our site to a retailer and buy a product or service, we may earn affiliate commissions. This layer typically consists of hardware such as the wireless hardware, i. Internet Layer Computer Networking. Recommended training: You may choose from various course formats to cover the objectives of the CompTIA Network+ certification exam. Hear all that and more on this episode of AONE.
Interview Questions and Answers
G TEC Tailored this course to build internationally recognized Professional certified with Microsoft, and Cisco. One of my favorite parts of this technology is SSH Tunnels. Are you an inspiring IT professional or a business owner that desires a better understanding of computer networks. Information Technology Education. There are no entry requirements for this qualification. 1 Background of the Study. There are many different topics, practice tasks, and simulations to choose from. ACME Anvil Company UC and UCCX Deployment. Learn the fundamentals of clean, effective Python coding and build the practical skills to tackle your own software development or data science projects. Upon completion, you will be well on your way to knowing exactly where you’re headed as a prospective networking professional and how best to get there. Other networking hardware used in computers includes data center equipment such as file servers, database servers and storage areas, network services such as DNS, DHCP, email, etc. Assuming enough resources are available i. 10 Method of Data Analysis 34. Because all or most items that are part of a network live in association or cooperation, almost any one of them can be referred to as a client. For example, if your undergraduate degree is Electrical Engineering, apply through the ECE Department. It covers networking technologies, protocols, the cloud, practical applications, and troubleshooting over six lessons including. This course is designed to provide a full overview of computer networking. College Campus Training. Still, others are drawn to this profession by the thrill of the hunt. Because networks need continuous monitoring and support, network administrators have indispensable roles in many organizations.
Employers
It is required when connecting to the internet via phone and using Voice over IP technology VoIP. It’s just shy of two hours long and consists of 24 brief lectures. While a router sends information between networks, a switch sends information between nodes in a single network. Gateway – A classic term for a router; a router at the edge of a network or enterprise internet; a multi layer protocol converter. Duration for Each Module. WiFi allows users to connect to the Internet at high speeds without the necessity of cables. During your final year, you will collaborate with other Software Development and Software Engineering students on a substantial project in a capstone course. Some of its advantages include, easy to install and reconfigure, less expensive than mesh, and performance is even despite the number of users. This course is offered for free by Udemy. Moreover, for this course, you must be comfortable with the implementation of the basic search algorithms and have a working knowledge of virtual machines and Linux. Information on how to become a member of the European Network; Name Surname Date of Birth Tc Identity Gender No Mobile Phone Email Country District Address Etc. Including Austin, Chicago, Denver, Houston, New York, San Francisco, Seattle, and Washington, D. Would you like to know if your Internet service provider actually provides the bandwidth they’ve promised. TLD Server The TLD server, like the root server, is part of the parsing process. While analysts don’t necessarily need graduate degrees, they can be an asset in workplaces where network analysts work closely with managers from other departments. While bandwidth has historically been stated in bits per second bps, current network cables have a significantly larger capacity, hence bandwidth is now more commonly expressed in megabits per second Mbps or gigabits per second Gbps. A traditional switch operates at Layer 2 of the OSI model. What’s being tested: Essential networking concepts; cabling, device, and storage technologies; managing networks; security; and troubleshooting methodology and tools. Pass with 104 112 UCAS Points from a QAA approved programme. ” Since the beginning, Google’s goal has been to develop services that significantly improve the lives of as many people as possible. Understanding Local Security Policies. The Network reference models were developed to allow products from different manufacturers to interoperate on a network. R1NPath 2 for, k=2 = R21, R22,. Are you the kind of person who can learn by watching videos. The Cisco CCNA Security curriculum provides a next step for individuals who want to enhance their CCNA level skill set and help meet the growing demand for network security professionals. With Cisco, for example, you’ll typically focus on equipment such as routers, wireless phones, switches, and security software. 1920×1200 16:10 aspect ratio. The IT team is having a disagreement on whether to use block storage or file storage for a network attached storage implementation. To register, click the course links above and select a start date.
Skill level
Noida, UP, 201301, India. You have left secondary education more than two years ago i. Net, Android, Hadoop, PHP, Web Technology and Python. Suppose Trudy positions herself in the network so that she can capture all the packets sent by Alice and send whatever she wants to Bob; she can also capture all the packets sent by Bob and send whatever she wants to Alice. Promo credit ends if eligibility req’s are no longer met; 0% APR. If you want to progress in your career, you should consider getting a master’s degree or, most importantly, a certification. Save my name, email, and website in this browser for the next time I comment. Western’s Computer Information Systems Program offers you a quality education in the area of network management, information technology and system analysis and design through synergistic teaching, research, and hands on learning. By the end of the course, students will know how to. Some familiar examples of application layer protocols, built on these lower protocols, are HTTP for accessing web content, SSH, and TLS/SSL. To view or add a comment, sign in. With the TCP server, there is a welcoming socket, and each time a client initiates a connection to the server, a new socket is created. Tuition includes full access to our interactive online classroom, self paced courses, and a wealth of reference materials, quizzes, learning exercises, and other tools to ensure you get an outstanding education. Initiates a secure and interactive file transfer session. Why a PhD from uOttawa may not be worth the paper it’s printed on. It costs around $399/ per year but is worth it because you get access to more than 7000+ courses and projects, and you can also get unlimited certificates. The program is highly customizable so students can tailor the curriculum to their career goals. Which of the following would the consultant identify as Single Points of Failure in need of upgrades for added redundancy. For more information:Cherme Lucero 919 866 5392. A mobile device management policy creates several essential benefits for an organization, like security measures and data and. Some of these professionals major in a closely related field. A switch is a multiport network device with a buffer and design that can improve its efficiency having a large number of ports means less traffic and performance. Following that, the OSI model’s seven tiers are discussed. Cisco ios Cookbook and Cisco ios in a Nutshell.
App PlatformBuild and Operate Cloud Native Apps
Students may select which exams they would like to count towards the Comprehensive Exam requirement. Learn more about how we use cookies by reading our Privacy Policy. Alice has to be in the top 4 neighbors of Bob for Bob to send out chunks to her; this might not occur even if Alice provides chunks to Bob throughout a 30 second interval. Protocol rules are based on the principles of civility— Dr. EcoLocate: A heterogeneous wireless network system for wildlife trackingfree downloadAll research to date using wireless networks for wildlife tracking has concentrated on monitoring a single species, using large GPS enabled collars. There are many different certifications available. Monali’s goal is to gain more experience in her field, expand her skill set, and do meaningful work that will positively impact the world. We’ll also cover the practical aspects of troubleshooting a network using popular operating systems. ASIC accreditation helps students and parents make a more informed choice and will also help a school, college, university, training provider or distance education provider, demonstrate to the international student body that they are a high quality institution. It reduces complexity and speeds up evolution. Taking extra classes in business, electrical engineering, and writing think project proposals and design specs gains you skills that can help you break into the computer networking field.
